
It is common practice to secure a file transfer server using firewall rules which only allow incoming connections from trusted partners.
Let's assume you have a US partner named "ACME Inc", connecting to your server from IP 1.1.1.1 using the user acme-inc, and another German partner called "AlleWerkzeuge AG", connecting to your server from IP 5.5.5.5 using the user alle-werkzeuge-ag.
You can configure your firewall to only allow connections from a list of trusted IPs like 1.1.1.1 and 5.5.5.5, but the firewall doesn't know about usernames. So it will allow the account acme-inc to connect even if the connection is initiated from 5.5.5.5, which is an IP outside of the ACME Inc network.
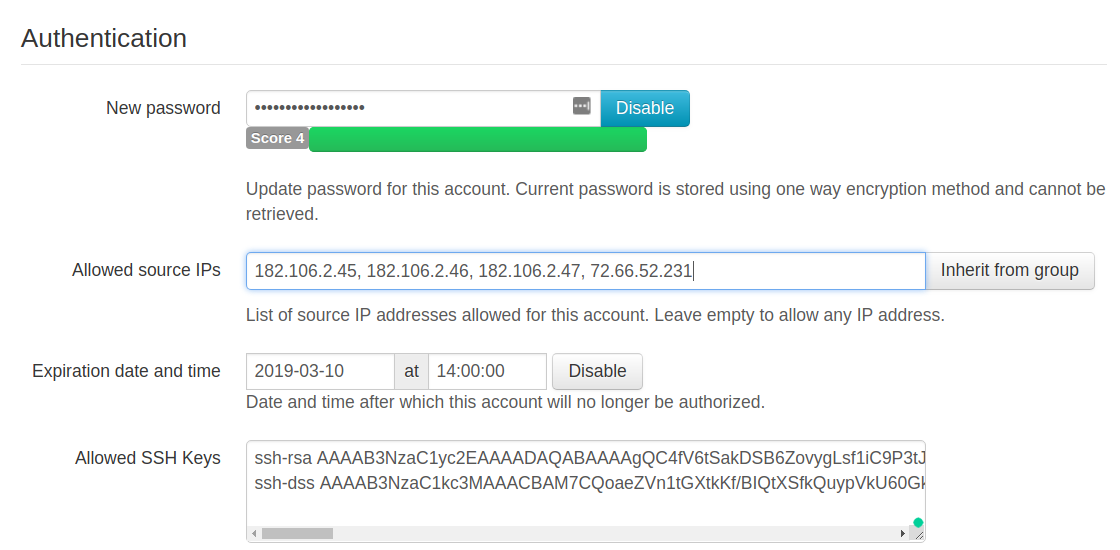
To complement firewall restrictions, SFTPPlus allows defining a fixed list of trusted IP rules from which it will allow connections for a specific user.
Such a configuration can be defined per user, but also per group, with multiple users inheriting their configuration from the group.
To restrict a specific user to connect through SFTP or FTPS to the file transfer server only from a certain IP (or IPs), you can use the source_ip_filter configuration option in SFTPPlus.
The remote access is denied when the user connects from a source address which is not whitelisted.
Below is a screenshot from our web-based management console demonstrating such a configuration.
Read more about securing your SFTP/FTPS and HTTPS services with SFTPPlus in our documentation page.