SFTPPlus Features and Product Tour
SFTPPlus MFT provides two components, the MFT Client and the MFT Server.
The components can run independently and as one, or integrate easily
with your existing infrastructure for file transfers.
SFTPPlus MFT Client Key Features
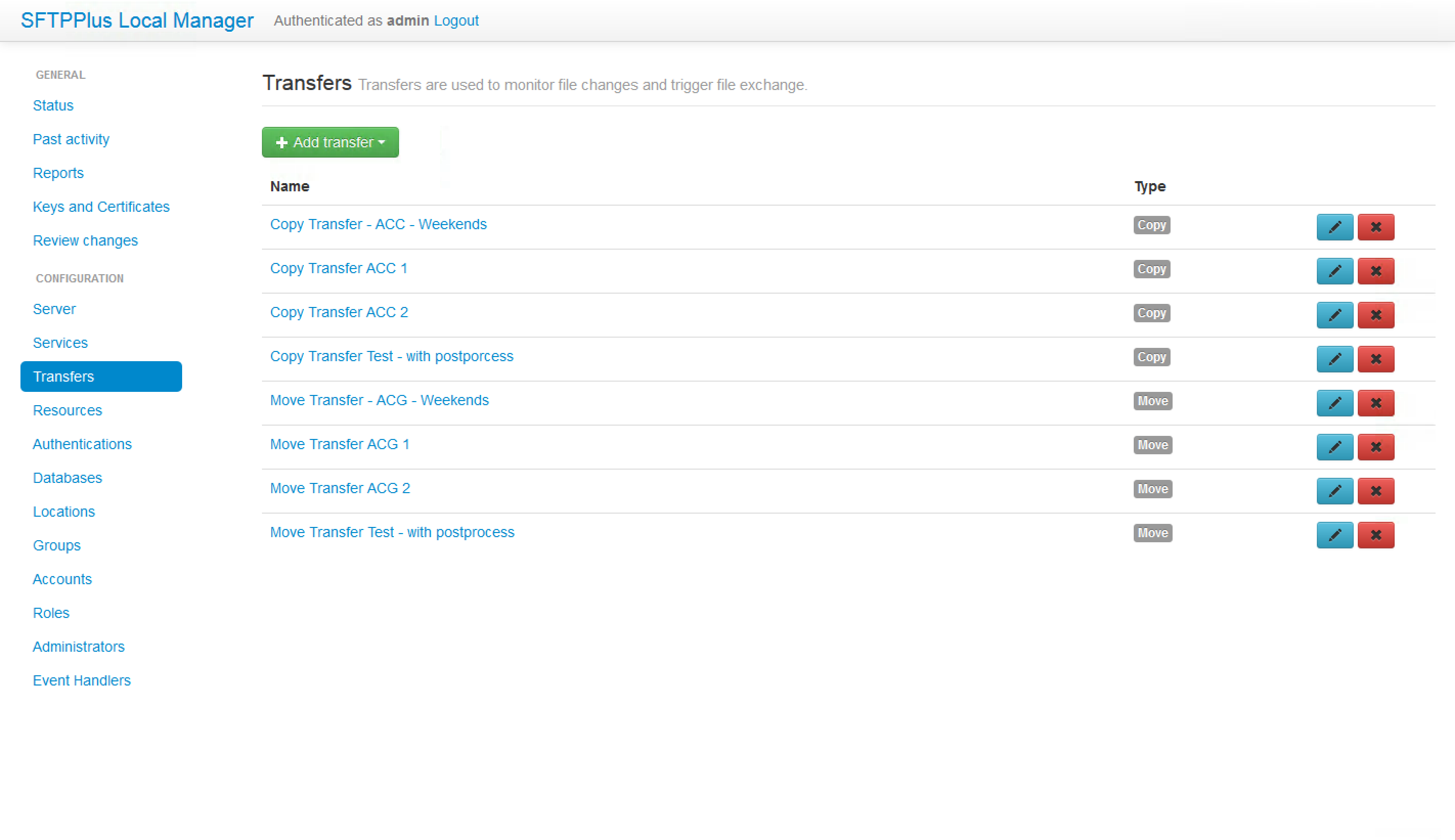
Managed Transfers
- Triggered and event-based transfers
- Scheduled transfers
- Events
- Pre- and post-processing
- External calls to arbitrary programs
Automation
- Local and remote files monitor
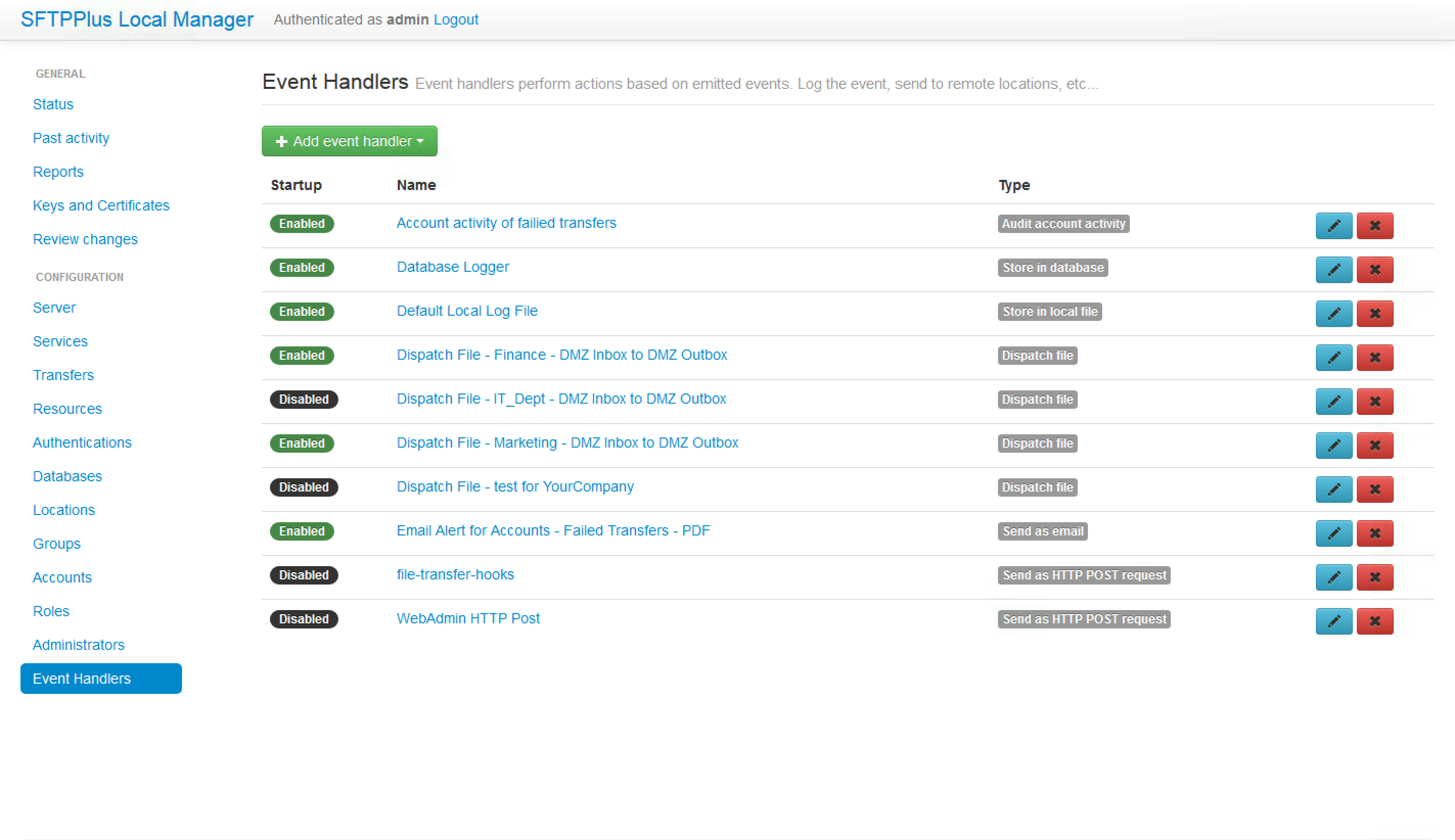
- Configurable actions based on triggers
- Configurable actions upon retries
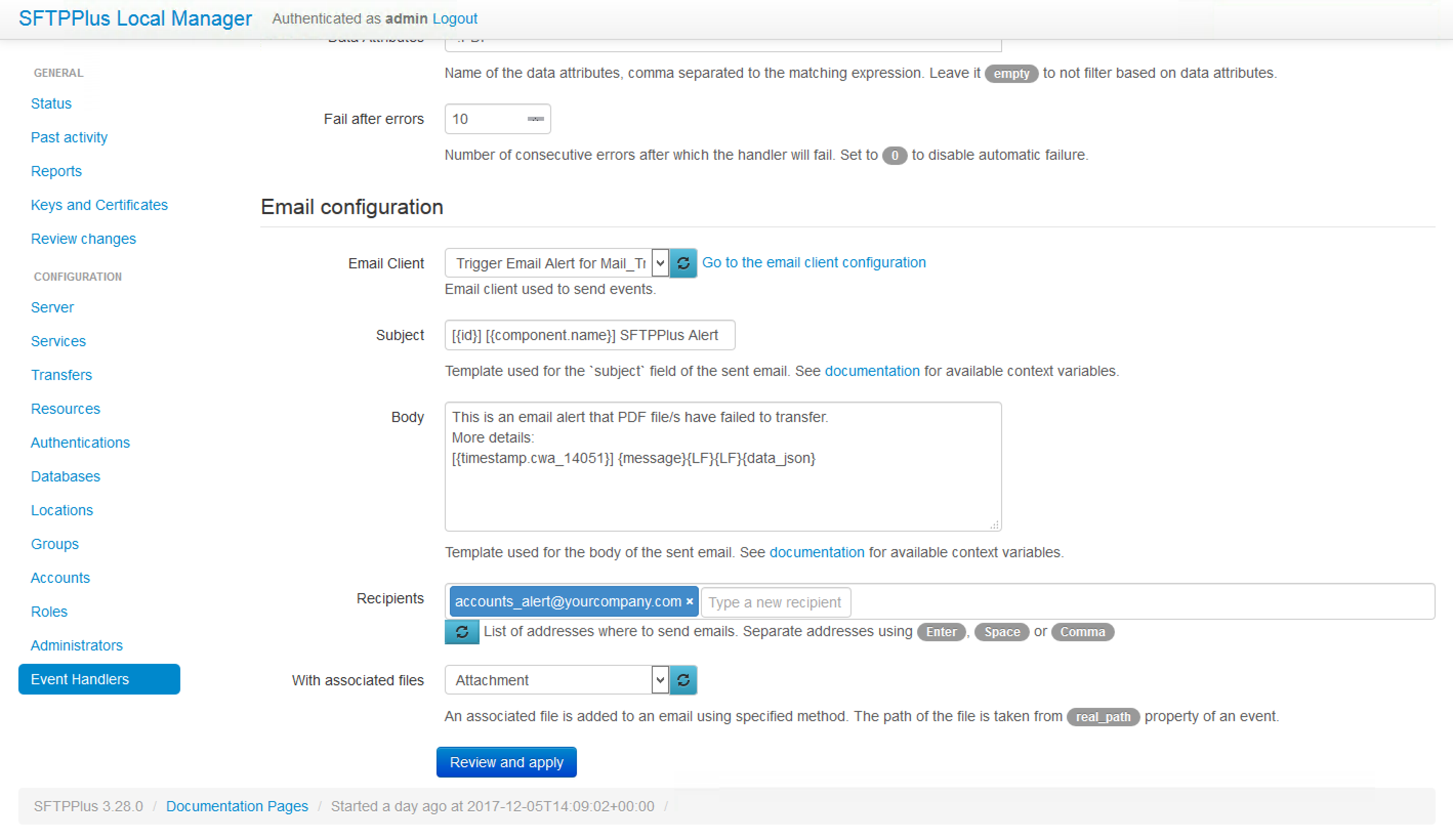
- Configurable alerts
- Encryption and decryption
- Text file configuration and non-interactive deployments
User Friendly
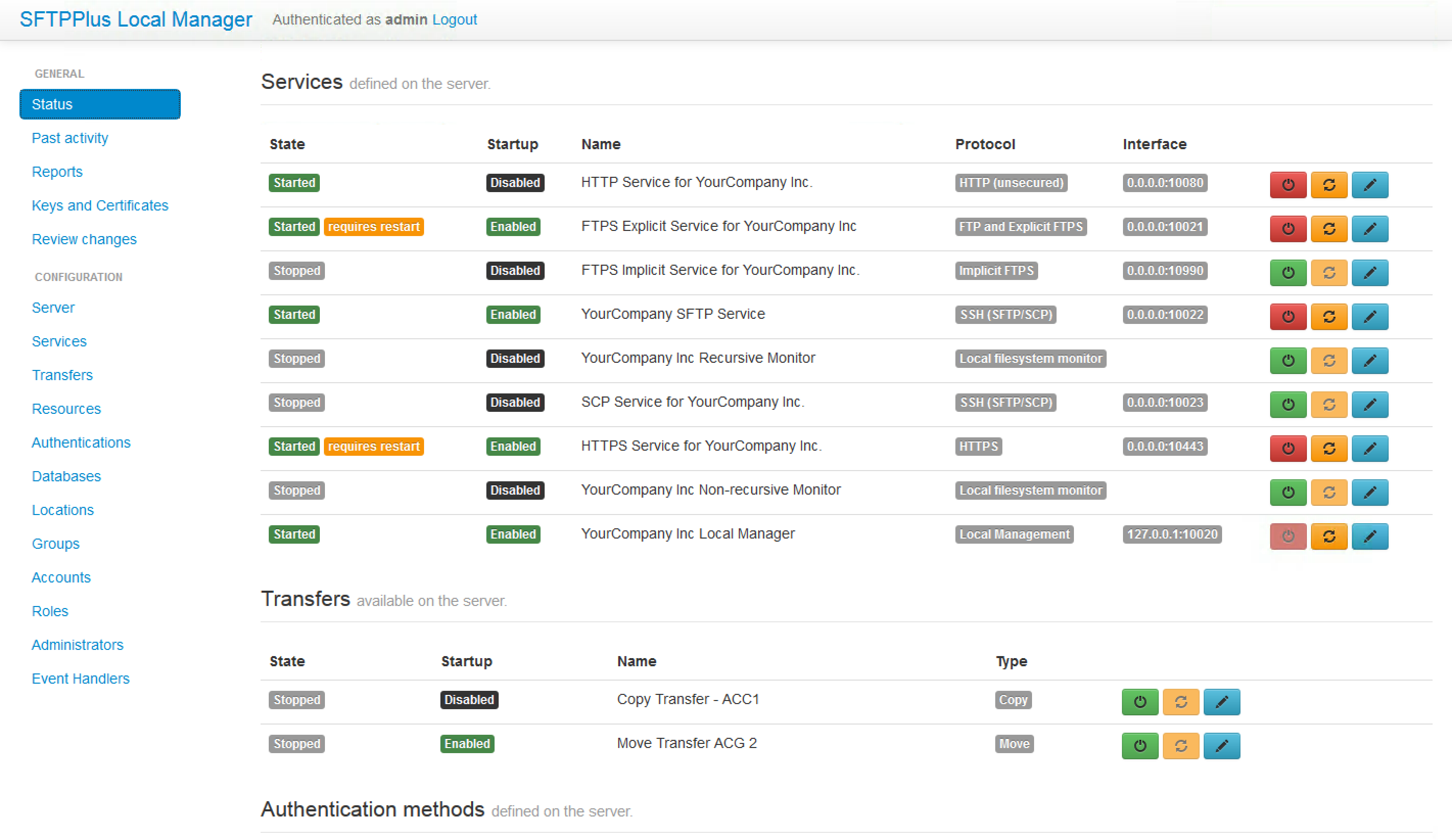
- Web administration interface
- Flexible service-based control panel
- Web interface for logging and audit trail
SFTPPlus MFT Server Key Features
Modular Server
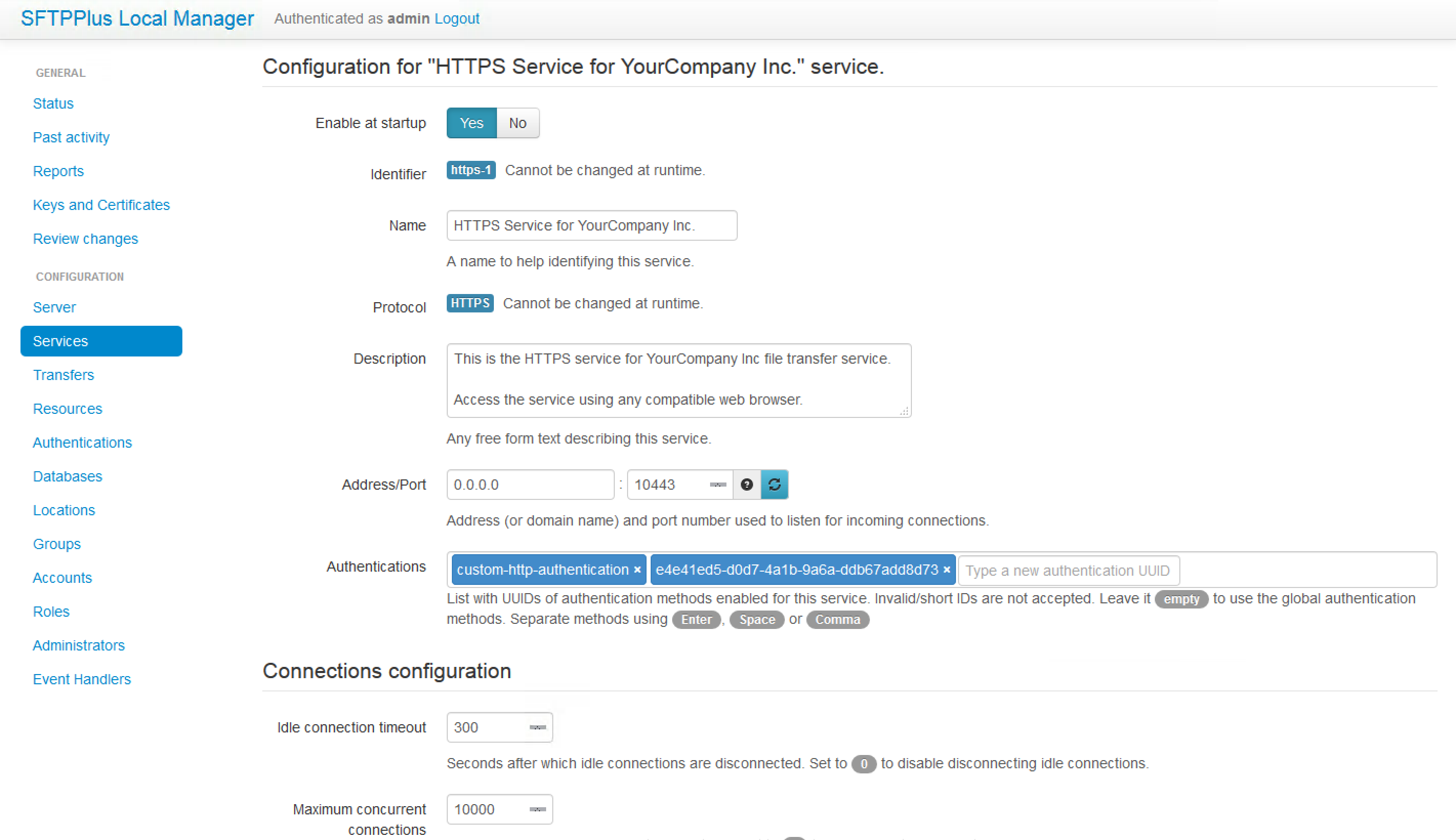
- Configurable protocol-based services
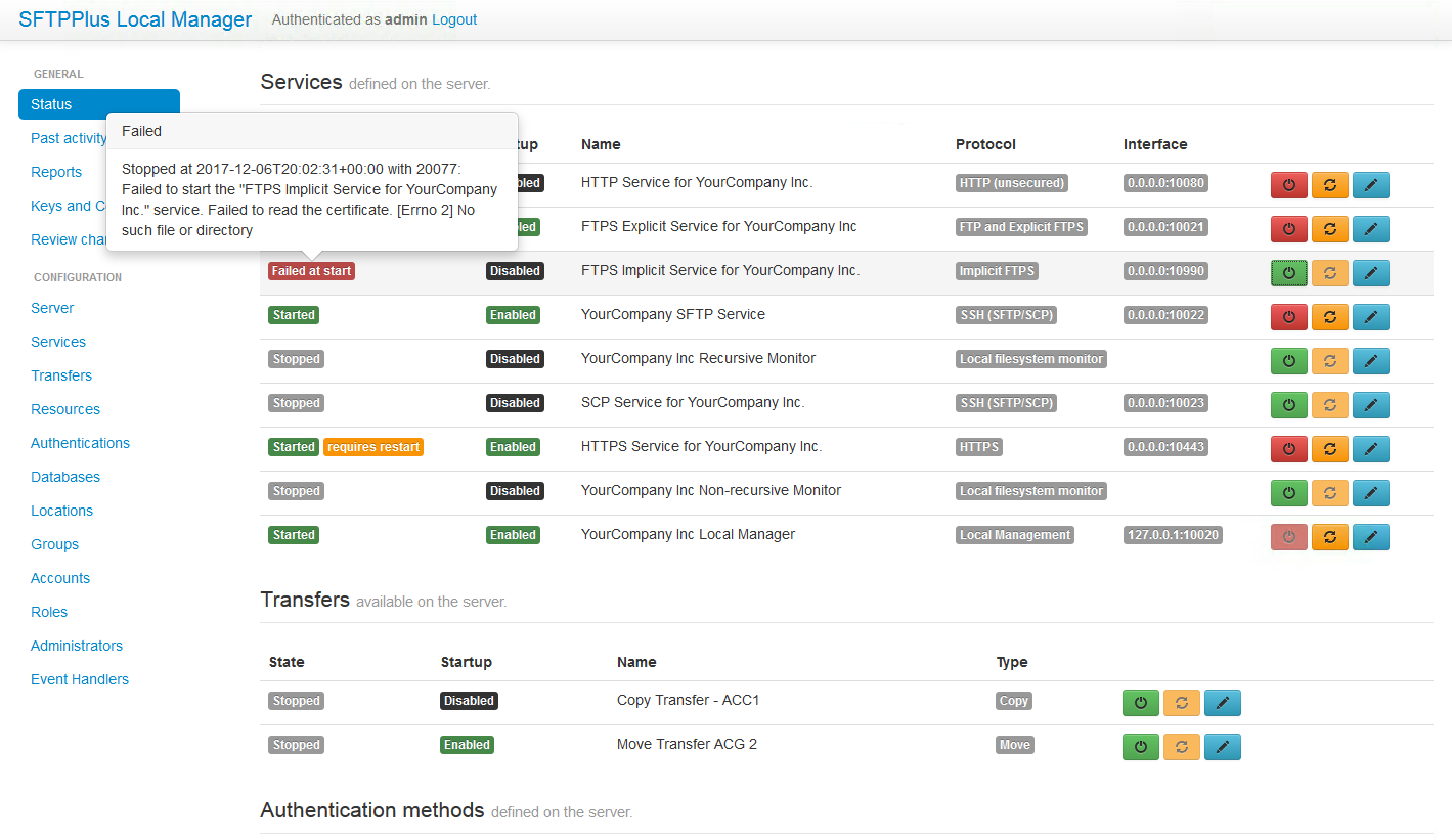
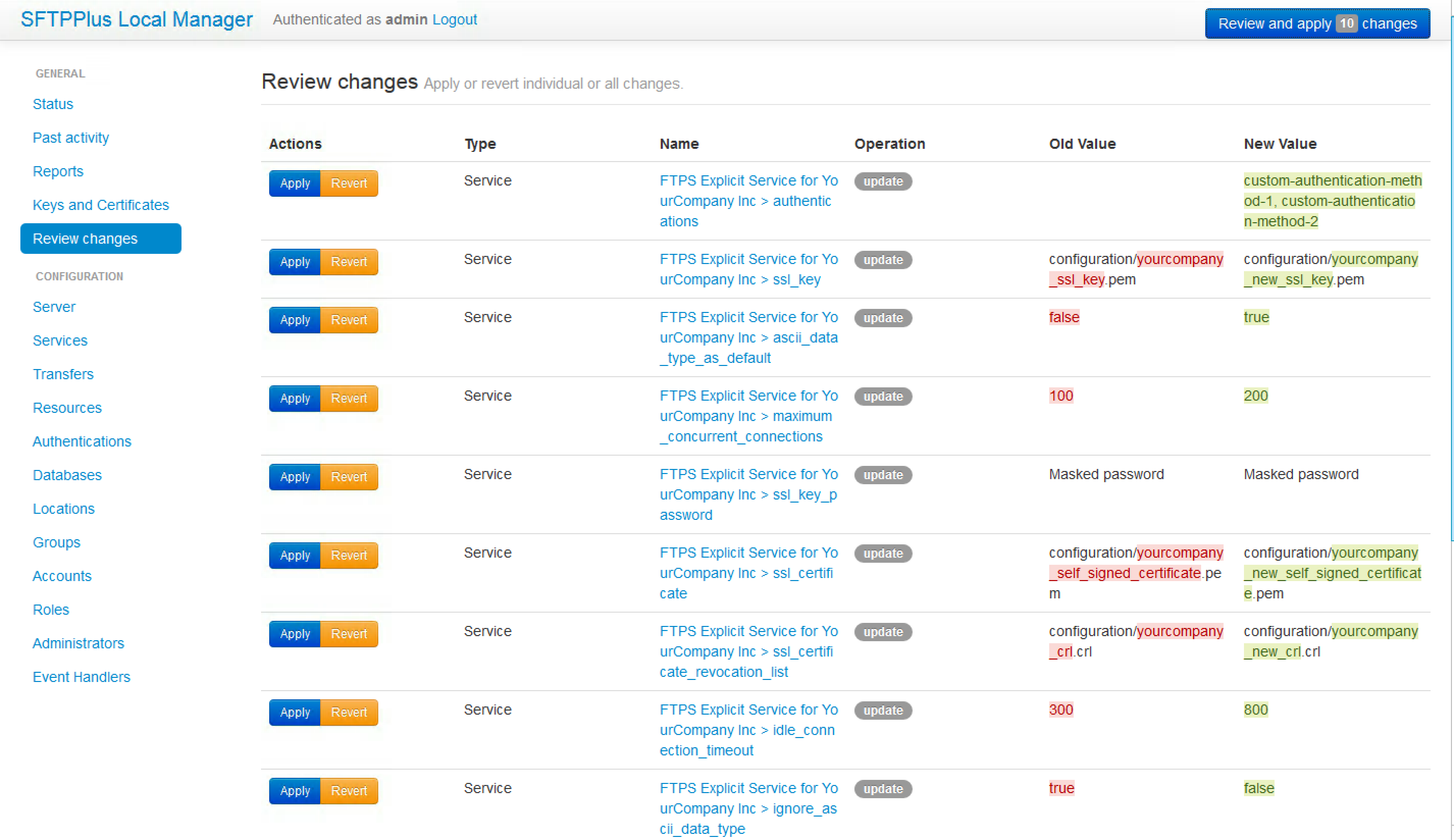
- Web-based administration panel
- Web-based SSL/TLS X509 management interface
- DMZ and user locking
- Configurable external program calls
User Friendly
- Web-based folder browsing and file downloads
- HTTP(S) API for pragmatic file management
- Actions and triggers for all protocols
SFTPPlus Key Features
Along with the key features our MFT Client and the MFT Server, both components include the following functionality.
Multiple Operating Systems
- Windows
- Linux Red Hat, Amazon, Ubuntu, Alpine, etc.
- macOS
- Kubernetes OpenShift, Rancher, EKS, AKS, GKE, etc.
- Docker and Containers ready
- Cloud ready
Multiple Protocols
- FTP
- Explicit FTPS / FTPES (over TLS)
- Implicit FTPS / FTPIS (over SSL)
- SFTP (over SSH version 2)
- AS2 over HTTP or HTTPS
- HTTP
- HTTPS
- WebDAV (over HTTPS)
- SCP (over SSH version 2) Only MFT Server
- Azure Files / Azure BLOB/ Azure Storage Only MFT Client
- SMB (Windows Share / CIFS) Only MFT Client
- Exchange Online / Outlook attachments Only MFT Client
- We are open to integrating new protocols
Secure and Extendable
- FIPS 140-2 ready
- HIPAA/HITECH ready
- ISO27001 ready
- GPG 13 ready
- Bespoken versions
- Public API Only MFT Server
- Software Development Kit (SDK)
Extensive Documentation
- Technical documentation for every version
- End-user guides with screenshots
- Configuration examples
Support and Quality Assurance
- Human assistance
- Free assistance during trial
- Thousands of automated tests
- Critical and security fixes are part of the Standard Support
- Long-term software support
- Consultancy and training services
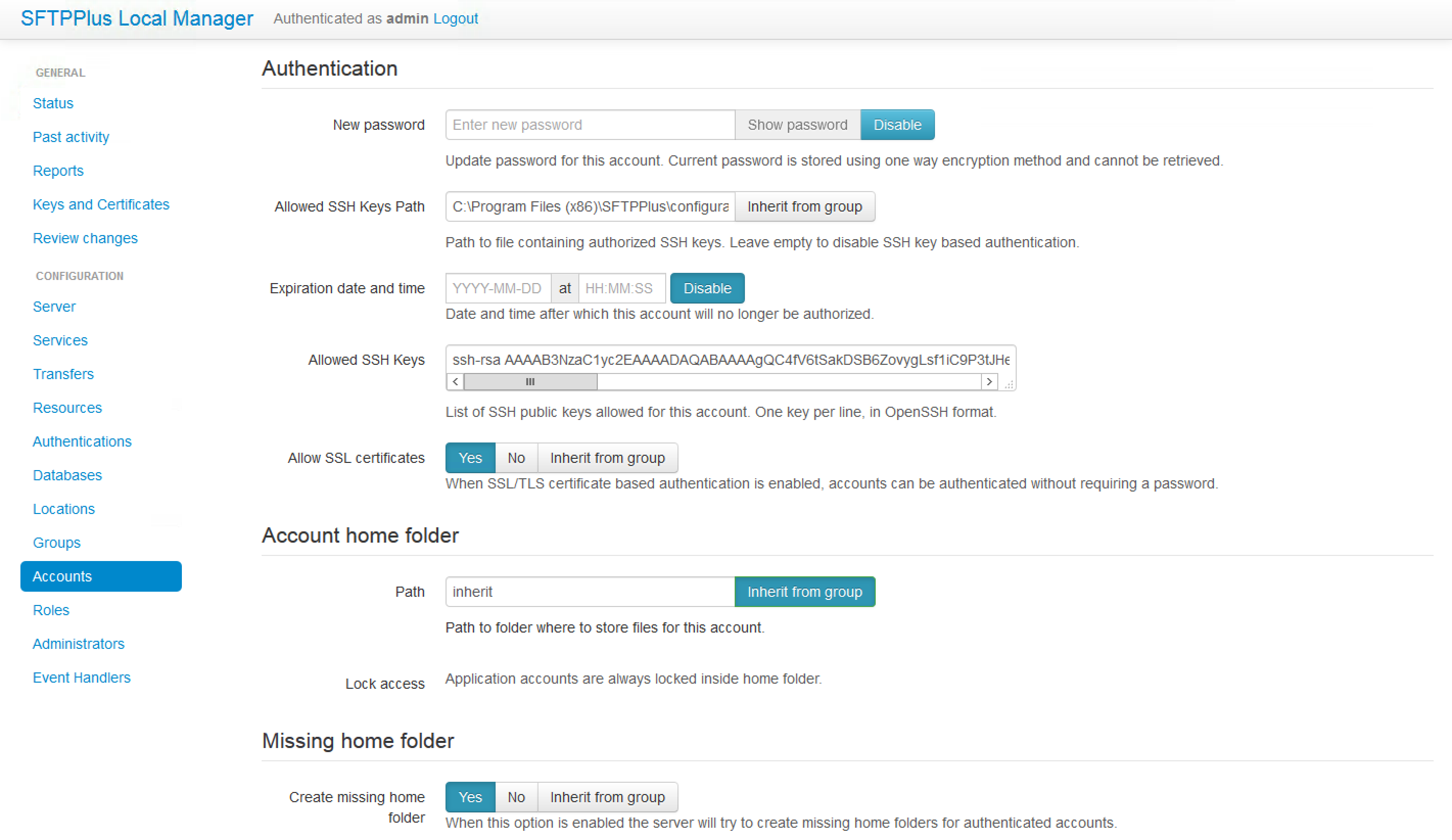
Authentication, Audit and Logging
- Structured logging inside a detailed audit trail
- Syslog, Windows EventLog, and SQLite persistent logging
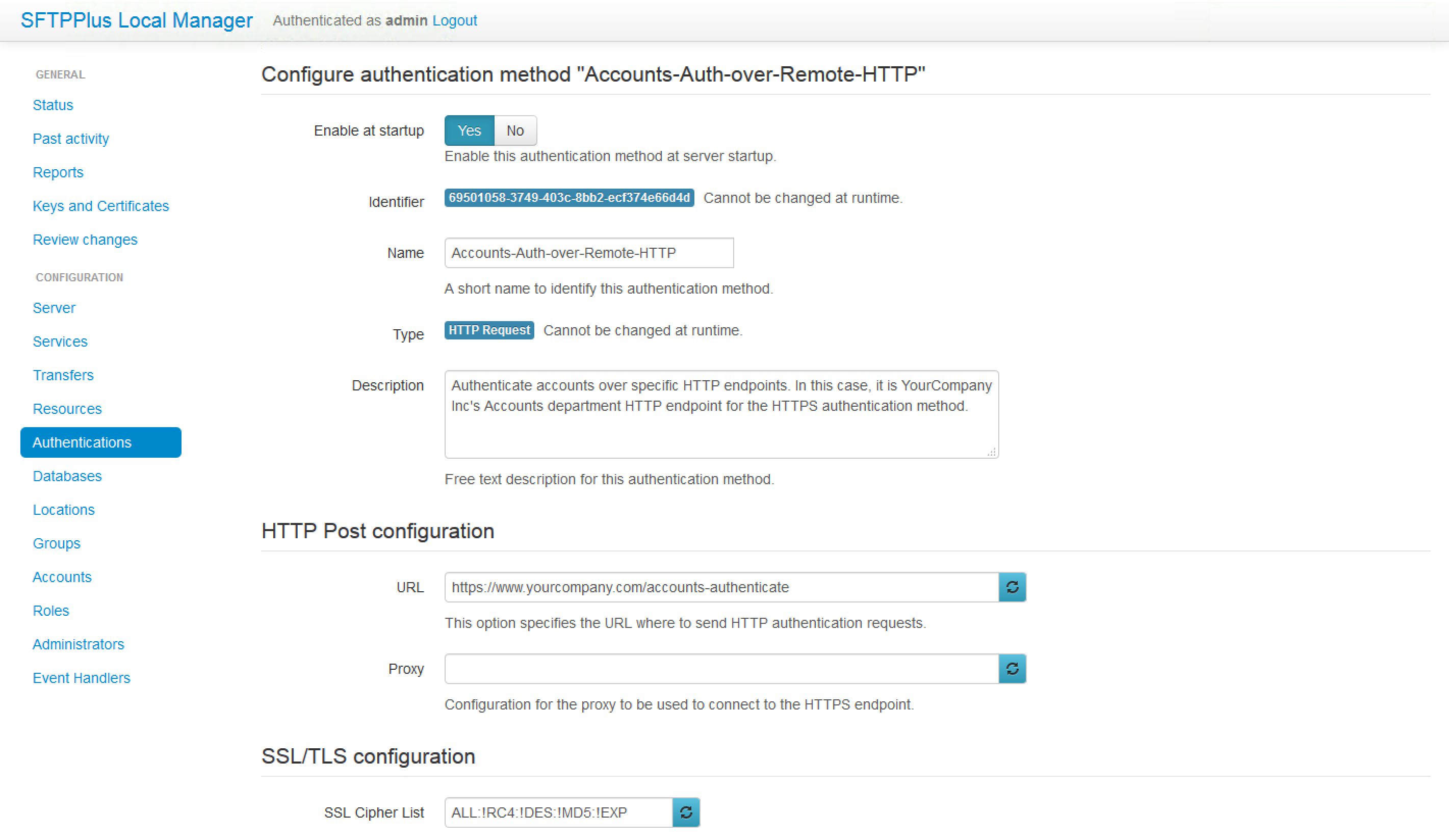
- Application level authentication
- Entra ID / Azure AD authentication
- OpenID Connect authentication
- LDAP and Active Directory authentication
- HTTP(S) authentication
Try our product (support included)
Product tour with screen captures
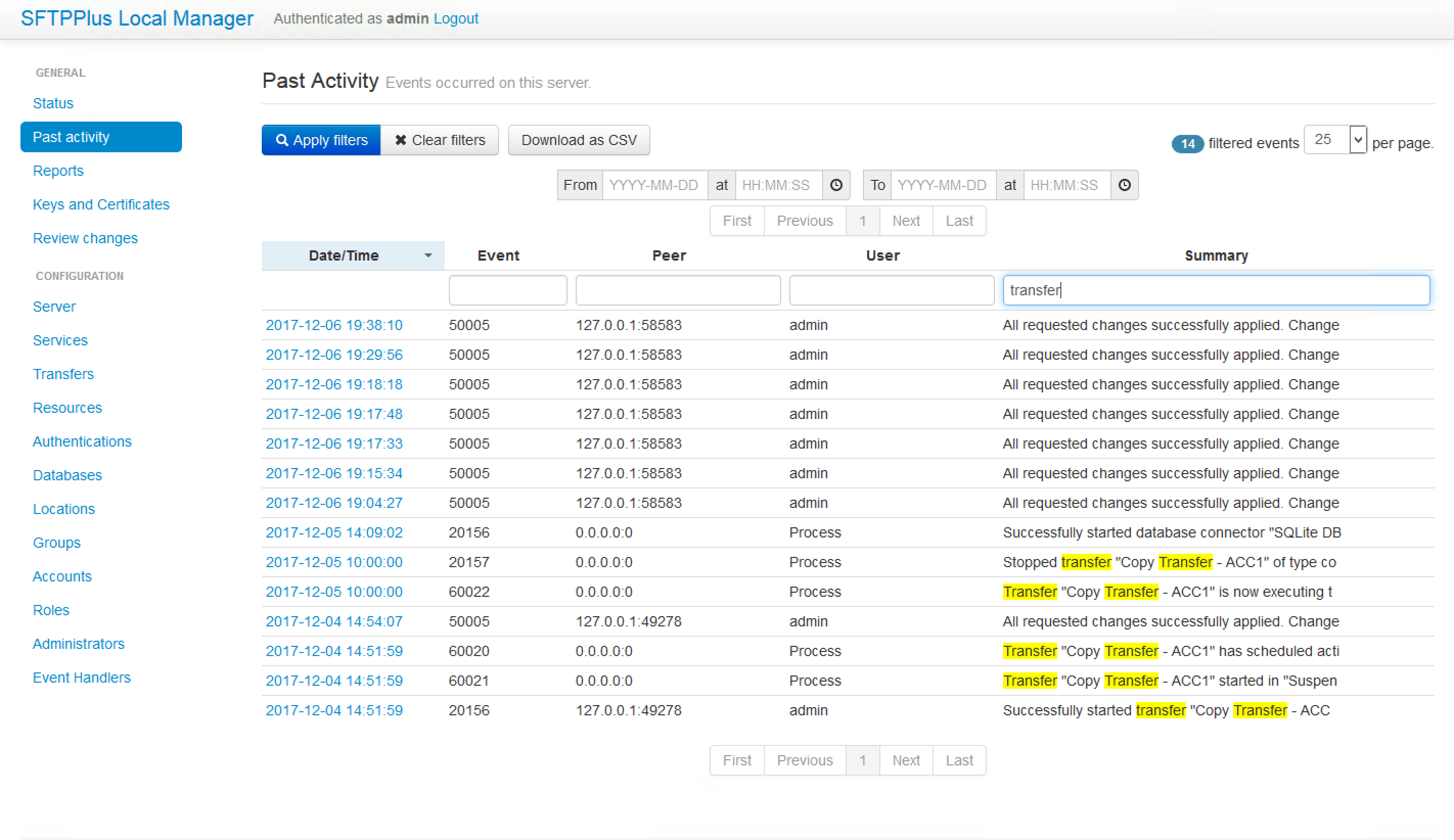 While operating, SFTPPlus will emit a set of events. Each event has a unique ID and defines a specific operation carried out by the server. The extensive audit trail is collated for system administration purposes such as monitoring activities. The trail will also help in meeting compliance requirements that involve logging of system activities.
While operating, SFTPPlus will emit a set of events. Each event has a unique ID and defines a specific operation carried out by the server. The extensive audit trail is collated for system administration purposes such as monitoring activities. The trail will also help in meeting compliance requirements that involve logging of system activities.