Efficient File Transfers with SFTPPlus MFT
Businesses depend on secure and efficient file transfer processes to support daily operations, partner collaboration, and compliance needs.
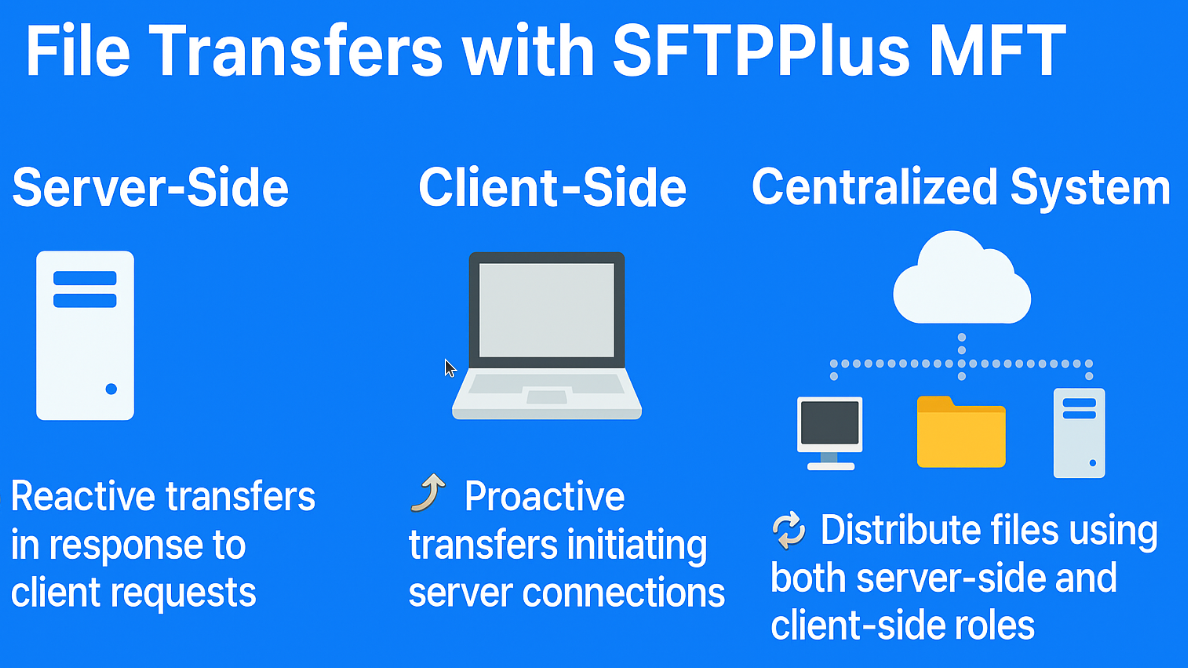
SFTPPlus MFT provides a platform to handle file transfers both as a server and as a client, enabling flexible integration into various environments.
This article explores how SFTPPlus MFT supports server-side, client-side, and combined deployments to create a centralized, reliable file distribution system. 🚀

Server-Side File Transfers - Reactive
When operating in server mode, SFTPPlus MFT acts as an endpoint that receives or serves files via standard protocols like SFTP, FTPS, or HTTPS. In this role, SFTPPlus waits for incoming connections or file uploads from partners, applications, or internal systems.
Server-side transfers are inherently reactive:
- Clients (e.g., partners or internal systems) initiate the connection.
- Files are uploaded to or downloaded from the server when the client requests it.
Use Cases:
- A supplier uploads invoice documents to a designated SFTPPlus folder.
- An internal user downloads processed EDI files using WinSCP.
- A cloud integration platform pulls data from the SFTPPlus server.
🔐 Security features like authentication, IP filtering, and file integrity checks make SFTPPlus MFT a strong choice for external-facing servers.
Client-Side File Transfers - Proactive
In client mode, SFTPPlus MFT acts as a file transfer initiator. It can connect to remote servers over protocols like SFTP, FTPS, or AS2, and send or fetch files based on scheduled jobs or file system events.
Client-side transfers are proactive:
- SFTPPlus actively monitors folders or triggers based on events.
- It connects to a target system and sends or retrieves files automatically.
Use Cases:
- SFTPPlus detects a new file in a staging folder and uploads it to a customer's AS2 endpoint.
- A scheduled job downloads batch reports from an upstream billing system.
- Files are periodically mirrored to a cloud storage location like Azure Blob or AWS S3.
🛠️ This proactive behavior is useful for automation, reducing manual interaction and improving consistency.
Combining Server-Side and Client-Side for Centralized transfers
One of SFTPPlus MFT's key strengths is its ability to operate as both a server and a client in the same deployment. This supports building a centralized file transfer distribution system.
Benefits of a Unified Deployment:
- ✅ Single point of control for incoming and outgoing file transfers.
- 🔁 Automatically route and forward files uploaded to the server.
- 🗃️ Apply automated actions like archiving, renaming, and notifications.
Example Scenario:
- 📥 A trading partner uploads a file to the SFTPPlus server.
- 🔄 A workflow detects the new file and triggers a client job.
- 📤 The file is forwarded to a third-party system via AS2 or SFTP.
- 📨 An MDN or delivery confirmation is logged and emailed to stakeholders.
With this combined approach, SFTPPlus becomes a hub for both external-facing transfers and internal processing pipelines.
Get support from experts
Whether you're building a secure file transfer portal for partners or automating internal workflows, SFTPPlus MFT provides a flexible, protocol-rich environment to support your needs.
Want to learn how to deploy SFTPPlus MFT in your environment?
Don't hesitate to contact our experts, and we'll provide the personalized support you need to optimize your file transfer processes with ease.